It takes a lot of resources to write code for software or a mobile application. The developers need to ensure that the end client receives the code without any intervention from any third party. They need to inform the client that the code has not been altered by any third-party. It is a tricky proposition to protect your codes online. Once you put it up on the internet, the codes are faced with a considerable risk from hackers. With 71% of fraud transactions happening through mobile apps and mobile browsers, users need to be assured that the apps they are downloading are safe. The answer to the conundrum is a Code Signing Certificate.
What is a Code Signing Certificate?
The reason for the rise of phishing attacks and malware over the internet is mainly due to the low levels of knowledge about internet security. Code signing is a process by which the developers can confirm that the script of software is secure and has not been altered through any unauthorized access by a third-party.
(Source: https://www.ssl2buy.com/wiki/what-is-code-signing-certificate-how-does-it-work)
The Code Signing Certificate is used by developers to digitally sign software programs, apps, and drivers. In this way, the end-user can verify that the code is authentic and has not been subject to unauthorized access by any third-party. It uses a 32-bit, or 64-bit digital signature and a certificate authority verify that the code has not tampered.
The need for a code signing certificate
In most cases, the browser does not download a code unless it is confirmed that it has not tampered. A certificate from a trusted Certificate Authority (CA) is needed. The certificate can create a trusted online sales entity apart from maintaining the authenticity and accountability of the underlying code.
Several reasons require a code signing certificate.
Once the developer of the code digitally signs the code, it is marked as authentic. The name of the author and the website is also mentioned. The certificate shows that the developer of the software can be trusted.
Scamsters can easily hack the software published online. Hackers can view the contents of the code and tamper with them. With the file being digitally signed, hackers will not have any access to the file. Moreover, without the certificate, browsers will alert users through popups.
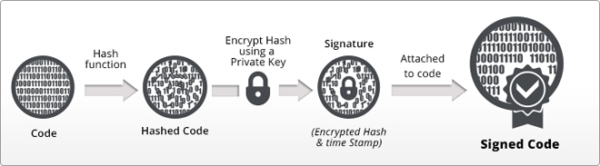
How does code signing work?
It works just like an SSL and starts with purchasing a certificate. The process begins with the CA verifying your identity. The process varies if you are an individual or a company. Next, you will install the certificate on the platform you are using. Though various platforms handle the signing process differently, the essence remains the same. You add your digital signature, which is a string of data that is hashed to show your identity and confirm the authenticity of the code.

(Source: https://www.digifloor.com/code-signing-certificates-verify-author-identity-16)
Once you have signed the code base, you can publish it online and allow a user can download the piece of code or software. If a user downloads the software, they will be provided with your digital signature that can display your identity as the developer and the authenticity of the code since it was published.
The process to verify the digital code signing signature in Windows
To check the digital signature, you can perform the following steps on the Windows system mentioned below.
- First of all, right-click the .exe executable file.
- Then select the “Properties” tab and then the tab “Digital Signatures”.
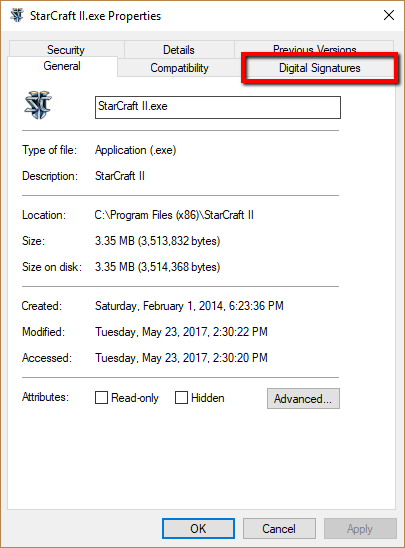
- Under the Signature list, select the concerned signature and click on “Details”.
- You can now view the information related to the Code Signing Certificate used.
- At the “Countersignatures” tab and within the “General” section the timestamp will be visible.

Conclusion
When we try to download software, we are apprehensive about its integrity. It is one of the reasons why developers must implement processes in place to ensure the integrity of the software that is downloaded by us. A Code Signing Certificate helps to authenticate the piece of code or software that we are downloading. The certificate is confirmation enough that the code has not been tampered with by any third-party.